
Mozilla blocked malicious Firefox add-ons installed by roughly 455,000 users after discovering in early June that they were abusing the proxy API to block Firefox updates.
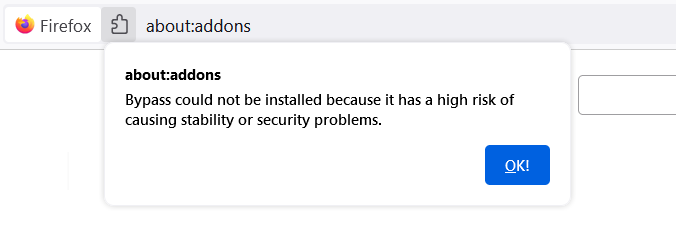
The add-ons (named Bypass and Bypass XM) were using the API to intercept and redirect web requests to block users from downloading updates, updating remotely configured content, and accessing updated blocklists.
"To prevent additional users from being impacted by new add-on submissions misusing the proxy API, we paused on approvals for add-ons that used the proxy API until fixes were available for all users," Mozilla's Rachel Tublitz and Stuart Colville said.
"Starting with Firefox 91.1, Firefox now includes changes to fall back to direct connections when Firefox makes an important request (such as those for updates) via a proxy configuration that fails.
"Ensuring these requests are completed successfully helps us deliver the latest important updates and protections to our users."
To block similar malicious add-ons to abuse the same API, Mozilla has added a system add-on (hidden from the 'about:addons' UI, impossible to disable, and updateable restartlessly) dubbed Proxy Failover.
Firefox users can see if they have the Proxy Failover add-on installed by going to the 'Firefox Features' section on the 'about:support' page.
This new add-on prevents attempts to interfere with update mechanisms in current and older Firefox versions.
While Mozilla didn't share if the two add-ons were doing anything else malicious in the background, BleepingComputer found after analyzing them that they likely were using a reverse proxy to bypass paywalled sites.
However, the add-ons also had Mozilla's domain in the paywall list which inadvertently also blocked browser updates.
A Mozilla spokesperson wasn't able to provide more details when contacted by BleepingComputer earlier today.
How to make sure you're not affected
Mozilla advises users to update their web browsers to at least the latest release version (Firefox 93), which can make sure that they're protected from add-ons abusing the proxy API.
"It is always a good idea to keep Firefox up to date, and if you’re using Windows to make sure Microsoft Defender is running. Together, Firefox 93 and Defender will make sure you’re protected from this issue," Tublitz and Colville added.
Microsoft Defender is the only anti-malware solution detecting the add-ons as malicious, tagging them as BrowserModifier:JS/BypassPaywall.A.
If you're not running Firefox 93 and have not disabled browser updates, you could be impacted by this issue. To make sure, try to update Firefox to the latest versions since it bundles an updated blocklist designed to disable these malicious add-ons automatically.
If you still can't update Firefox, you also have the option to find the add-ons that block you from upgrading to a newer version and remove them by going through these steps:
- Visit the Troubleshooting Information page.
-
In the Add-ons section, search for one of the following entries:
Name: Bypass
ID: {7c3a8b88-4dc9-4487-b7f9-736b5f38b957}
Name: Bypass XM
ID: {d61552ef-e2a6-4fb5-bf67-8990f0014957}
NOTE: Make sure the IDs match exactly as there might be other, unrelated add-ons using those or similar names. If none of those IDs are shown in the list, you are not affected.
If you want to ensure that there are no traces left, you can also refresh Firefox to reset all add-ons and settings or start from scratch by downloading and installing a new copy of Firefox.



Comments
TsVk! - 2 months ago
The plugins are dubious in nature in the first place, basically allow users to steal paid content.
Like warez and cracked software these sort of things are a goldmine for hackers, and in some peoples opinion land in a moral grey area.
Melionix - 2 months ago
There's always going to be those that give the middle finger to capitalism and the idea of paying for absolutely everything, especially if you live in a country like India where the salaries are zilch.
m-p-3 - 2 months ago
There's an open-source addon that actually does just that, at least if you don't trust it you can inspect its code easily
https://github.com/iamadamdev/bypass-paywalls-chrome (also for Firefox, despite the name of the repository)
TanyaC - 2 months ago
Any add on that stops mozilla forcing updates on users is a good thing imo, but I do agree these add ons were malicious in nature.
Bleeter - 2 months ago
Use policies to block autoupdates if you need to, no need to use addons for that.